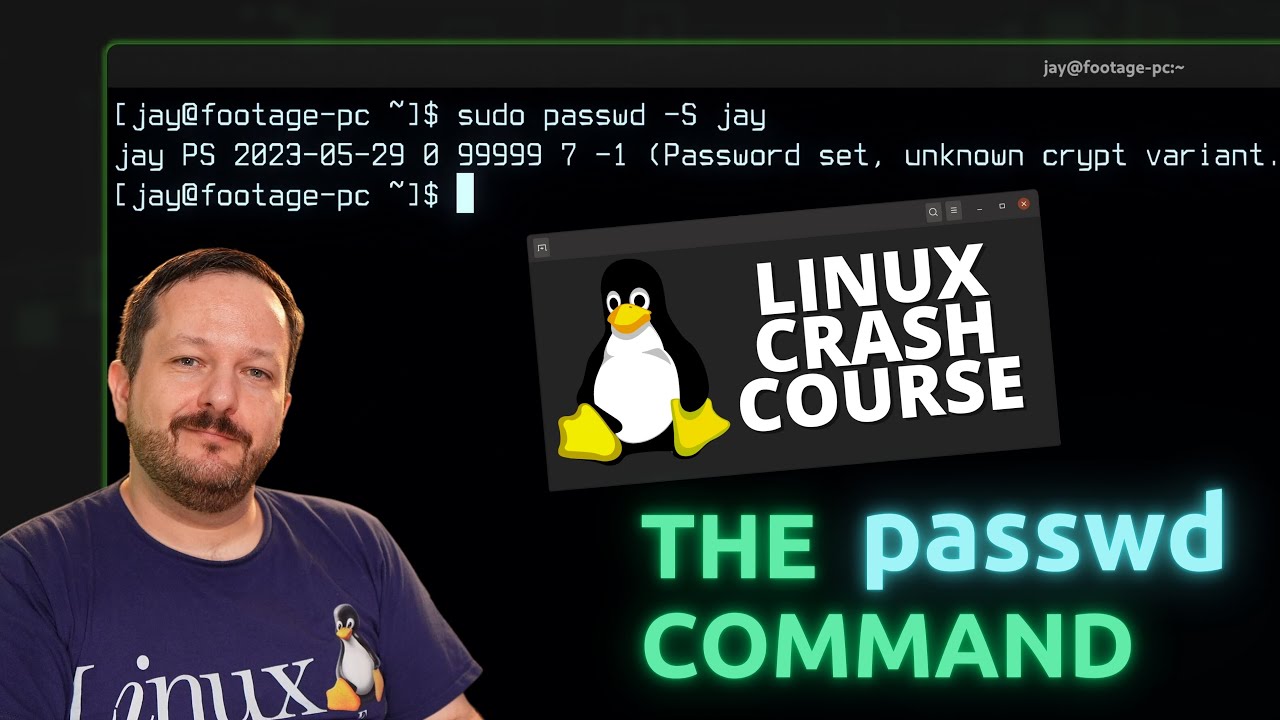
The passwd command is what you use to change your password on your Linux system, but did you know you can also use it to change the password of other users, lock accounts, and view statistics? In this video, you’ll learn about the passwd command – and there may even be a new thing or two to learn even if you’re already familiar with the command.
(more…)